In the realm of cybersecurity, organizations rely on ratings to gauge their security posture and make informed decisions. However, there are instances where the cybersecurity rating might not accurately represent the true state of an organization’s defenses – this can stem from misattributions of assets to your business, lack of updates to consider remediations and mitigations, inclusion of assets from a divested department or business unit and other scenarios. This article delves into the common reasons behind inaccurate cybersecurity ratings, shedding light on the complexities that can lead to misinterpretations and misalignments.
The Illusion of a Single Metric
Security ratings, and particular legacy security ratings providers, often give the impression of a single, definitive metric. However, that single metric rating is based on many factors which may be inaccurately represented, each contributing to the overall score. An overemphasis on the rating number itself can lead to misunderstandings, as organizations might overlook specific areas where improvements are needed. How a security rating is created often relies on lots of external data and passively collected data about an organization, but there are alternative providers with differing methodologies.
Many security ratings vendors do not do a respectable job of incorporating the context of an enterprise. An opportunity is to look for a security rating vendor, like FortifyData that provides contextualized security ratings that enable enterprises to classify assets, accept risk and manage likelihood and business impact adjustments to arrive at a more accurate risk representation as portrayed by the security rating.
Additional Resources
Cybersecurity rating scale explained
What are security ratings used for?
How are security ratings created?
What is a good cybersecurity rating?
How do you improve your security rating?
Is it easy to switch security ratings providers?
What Kind of Company is BitSight?
Select What are the 5 C’s of Cybersecurity?
What is the Highest Security Rating?
What is the difference between SecurityScorecard and BitSight?
What is the difference between BitSight and RiskIQ?
Read the Whitepaper
The Evolution of Cybersecurity Ratings and How They Can Boost Risk Visibility
Reasons for a wrong or low security rating
Data Inaccuracy and Incompleteness: Ratings are generated based on data collected from various sources, including externally observable data points. If these data sources are inaccurate (including misattributed assets), outdated, or incomplete, the resulting rating may not accurately reflect the organization’s security posture.
Reliance on External Data: Cybersecurity ratings often start with, and some providers only rely on, externally gathered data, such as indicators of compromise and observed compromised systems. This reliance can lead to discrepancies, as internal security practices and controls that are not publicly disclosed might not be fully accounted for. Therefore, the rating might not reflect the entirety of an organization’s security efforts.
Lack of Contextual Insight: A common pitfall is the lack of contextual insight in cybersecurity ratings. An organization’s security rating might not consider industry-specific threats, regulatory compliance, or internal security policies that influence an organization’s security effectiveness. Without this context, the rating might misrepresent an organization’s true level of preparedness. Review our note about context-based security ratings above.
Misalignment with Internal Assessments: Organizations often conduct internal assessments to evaluate their security posture. These assessments might not align perfectly with the external cybersecurity rating due to inaccurate external asset identification, leading to confusion. The methodologies and criteria used in internal assessments might differ from those used by the rating platform, resulting in discrepancies and inaccuracy in the security rating.
Rapidly Evolving Threat Landscape: The cybersecurity landscape is constantly evolving, with new threats emerging regularly. Some security ratings providers are known to lag in the updates of security ratings they provide for organizations. A high cybersecurity rating today might not necessarily reflect the same level of security tomorrow. Rapidly changing threat vectors can render a seemingly accurate rating obsolete within a brief period.
Improper Data Interpretation: Even if the rating is accurate, improper interpretation can lead to misalignments. Stakeholders might misinterpret a rating as an indicator of complete security, failing to recognize that a rating is a snapshot of a moment in time and does not account for potential vulnerabilities. The security rating can ebb and flow along the security rating scale based on changes in landscape, vulnerabilities and remediations thus needing steady communication with stakeholders to understand that the measurement as represented by the security rating is a dynamic metric.
The accuracy of a cybersecurity rating is influenced by a multitude of factors, ranging from data quality to contextual understanding. Organizations must recognize that a security rating is not a standalone metric but rather a reflection of a complex set of variables. To ensure that the rating accurately represents an organization’s security posture, it’s crucial to validate the accuracy of data sources, contextualize the rating within the organization’s specific landscape, and consider internal assessments alongside external ratings. Embracing a holistic approach to cybersecurity assessment is essential for building a resilient and adaptable security strategy that remains aligned with the evolving threat landscape.
Looking for an accurate security rating?
FortifyData provides a trusted and accurate security rating based on weekly external attack surface assessments of your confirmed IT asset inventory. We consider asset classification, likelihood adjustments and compensating controls and enrich the findings with dark web discoveries and cyber threat intelligence to give you a contextualized security rating.
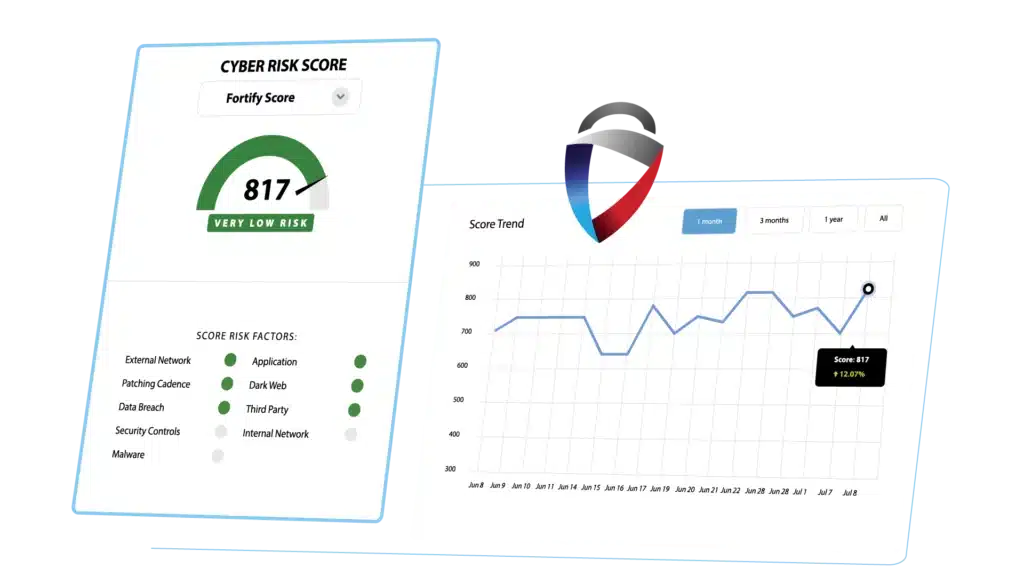
FortifyData is an industry-leading Continuous Threat Exposure Management (CTEM) company that enables the enterprise to manage cyber risk across the organization. By combining automated attack surface assessments with asset classification, risk-based vulnerability management, security ratings and third-party risk management, you get an all-in-one cyber risk management platform.

