
The Canvas Breach Is a Third-Party Risk Story. Treat It Like One. The Instructure Canvas breach that unfolded across the…
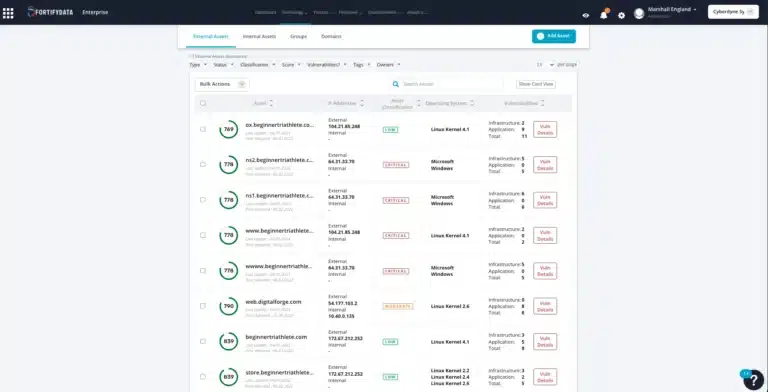
Are you tired of spending too much time trying to make sense of the vast number of vulnerabilities that your organization is exposed to? Cut through the noise and get a view of the vulnerabilities with the most impact that actually matter. FortifyData’s Cyber Risk Management platform uses a prioritized risk approach that considers context through asset classification, threat likelihood, and business impact, so you know where to focus time and resources on the most critical vulnerabilities to your organization.
Traditional vulnerability management tools focus on discovering vulnerabilities without context, and then rank them by a generic CVSS score. This approach burdens your team with manual analysis to determine what is important to the organization. Using this traditional approach misdirects resources to remediating high CVSS score vulnerabilities on assets that are not critical to the business or that do not consider custom mitigation or compensating controls. FortifyData prioritizes vulnerabilities, both internal and external, based on aspects unique to your organization – through asset classification and contextualization – so you get a true view of what is important.
The FortifyData platform integrates threat intelligence feeds that are updated hourly, so you get immediate prioritization of risks according to threats against the industry and technologies. Information such as the threat groups and trending threats like malware variants that are targeting the Higher Education industry.
The threat intelligence feed data is integrated into our risk prioritization, so as threat intelligence changes – related to susceptible assets you have, increase in activity against the industry and threat signatures – the FortifyData platform analysis takes this into account for the threat likelihood calculation and adjusts your risk prioritization accordingly.
Ready to see the active threats?
This eBook, written by SC Media, explains the benefits and explores how to set up an integrated cyber risk management solution for your organization.




