Threat Groups Actively Targeting Higher Education Institutions
Jan. 2023 Threat Advisory
Summary
Threat intelligence can provide valuable insights into the latest vulnerabilities being actively exploited by cybercriminals, as well as the potential impact these vulnerabilities could have on your organization. This information can help you prioritize vulnerabilities and determine the most effective patching or mitigation strategies.
Threat actor group activity against Higher Education institutions increased in Q4 2022.
This report looks at those active groups, their motivations and some of the known vulnerabilities the groups are exploiting within Higher Education networks and systems. This report examines cyber threat intelligence data available in the FortifyData platform. FortifyData incorporates threat intelligence data for threat likelihood enrichment capabilities, helping security teams at universities and colleges better prioritize risks and vulnerabilities across networks and IT assets. The FortifyData platform informs risk through incorporation of intelligence sources like AlienVault’s OTX, Cybersecurity and Infrastructure Security Agency (CISA), MITRE ATT&CK and many other threat intelligence sources.
Active Threat Groups
This report covers ongoing activities of threat groups from starting October 2022 through Jan 2023. During this time there was activity from 18 threat groups identified with related activities specifically targeting Higher Education institutions. Motivations for these groups are classified among financial gain increasingly from malware campaigns, espionage, IP and Research data theft and compromising supply chains. We have aggregated the information to illustrate the groups, their motivations and known CVEs, noting any overlap.
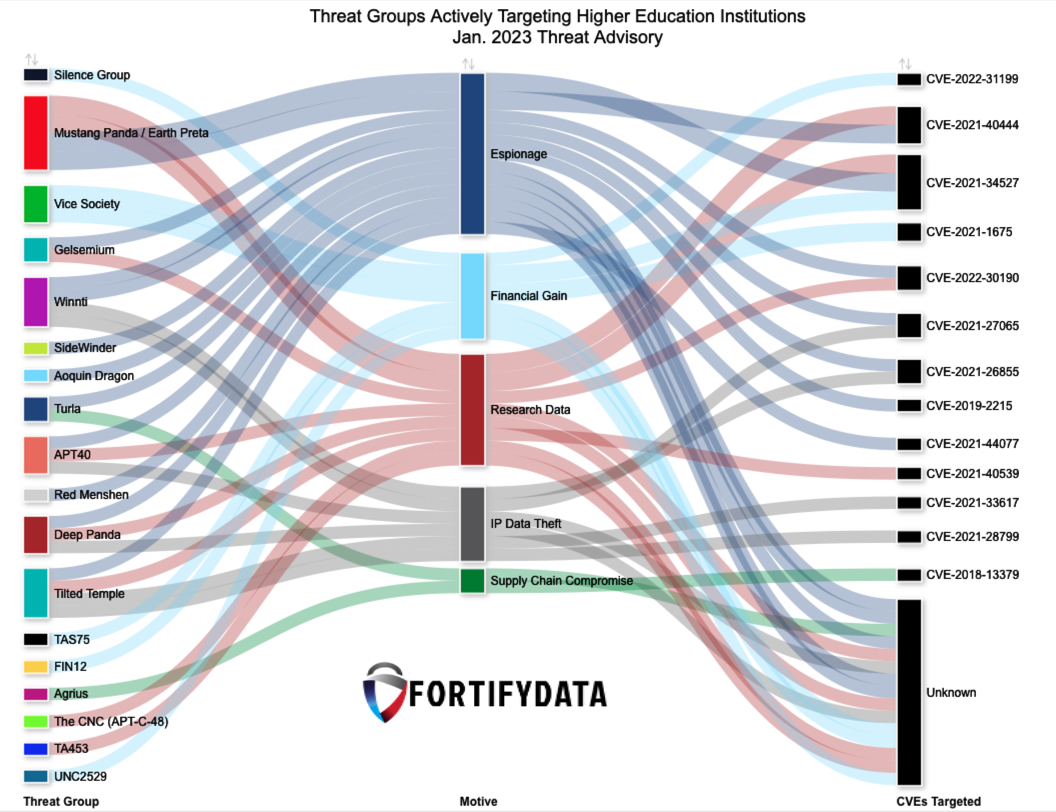
The known CVEs employed by the threat groups vary with only some overlap among certain vulnerabilities, as identified through internal scanning assessments. PrintNightmare (Windows Print Spooler Remote Code Execution) is one CVE being targeted by two different groups, Vice Society and Mustang Panda as part of their efforts of espionage, financial gain and research theft.
The CVEs targeted range from ‘Medium’ to ‘Critical’ based on CVSS 3.0 scoring. Higher Education Institutions must utilize a process to prioritize vulnerability identification and remediation of affected assets using data from this threat advisory report.
An important question to ask your vulnerability management team is “Does your current vulnerability management system uses more than just CVSS and auto-prioritize vulnerabilities using informed industry threat intelligence data, and asset criticality?”. CVSS scores are just not sufficient, as the pace of threat activity within your industry is vital to remain proactive with effectively resolving issues that matter most to your institution. Automating these processes will help scale your vulnerability and remediation management program.
Higher Education Targeted CVEs and Threat Actors Involved
| CVE | Description | CVSS 3.0 | Actors Targeting CVEs |
|---|---|---|---|
| CVE-2022-31199 | Remote code execution vulnerabilities exist in the Netwrix Auditor User Activity Video Recording component affecting both the Netwrix Auditor server and agents installed on monitored systems | 9.8 | Silence Group |
| CVE-2021-4044 | Microsoft MSHTML Remote Code Execution | 7.8 | Mustang Panda / Earth Preta |
| CVE-2021-34527 | Windows Print Spooler Remote Code Execution Vulnerability | 8.8 | Mustang Panda / Earth Preta |
| CVE-2021-1675 | Windows Print Spooler Elevation of Privilege | 8.8 | Mustang Panda / Earth Preta |
| CVE-2022-30190 | Microsoft Windows Support Diagnostic Tool (MSDT) Remote Code Execution | 7.8 | Gelsemium |
| CVE-2021-27065 | Microsoft Exchange Server Remote Code Execution | 7.8 | Winnti |
| CVE-2021-26855 | Microsoft Exchange Server Remote Code Execution | 9.8 | Winnti |
| CVE-2019-2215 | Vulnerability in the MySQL Server product of Oracle MySQL (component: Server: Stored Procedure). Supported versions that are affected are 8.0.23 and prior. | 4.9 | SideWinder |
| CVE-2021-44077 | Zoho ManageEngine ServiceDesk Plus before 11306, ServiceDesk Plus MSP before 10530, and SupportCenter Plus before 11014 are vulnerable to unauthenticated remote code execution. | 9.8 | Tilted Temple |
| CVE-2021-40539 | Zoho ManageEngine ADSelfService Plus version 6113 and prior is vulnerable to REST API authentication bypass with resultant remote code execution. | 9.8 | Tilted Temple |
| CVE-2021-33617 | Zoho ManageEngine Password Manager Pro before 11.2 11200 allows login/AjaxResponse.jsp?RequestType=GetUserDomainName&userName= username enumeration, because the response (to a failed login request) is null only when the username is invalid. | 5.3 | Tilted Temple |
| CVE-2021-28799 | An improper authorization vulnerability has been reported to affect QNAP NAS running HBS 3 (Hybrid Backup Sync. ) If exploited, the vulnerability allows remote attackers to log in to a device. | 9.8 | Tilted Temple |
| CVE-2018-13379 | An Improper Limitation of a Pathname to a Restricted Directory ("Path Traversal") in Fortinet FortiOS 6.0.0 to 6.0.4, 5.6.3 to 5.6.7 and 5.4.6 to 5.4.12 and FortiProxy 2.0.0, 1.2.0 to 1.2.8, 1.1.0 to 1.1.6, 1.0.0 to 1.0.7 under SSL VPN web portal allows an unauthenticated attacker to download system files via special crafted HTTP resource requests. | 9.8 | Agrius |
Auto-Prioritize Vulnerabilities with Risk-based Vulnerability Management
The FortifyData platform uses risk informed intelligence presented above incorporated with external and internal vulnerability assessments to auto-prioritize risks and vulnerabilities within your institution. Additional context such as asset criticality is also considered during the assessments. The system does this on your behalf, so you don’t have to manually review and prioritize every vulnerability using published threat intelligence – unless you really love doing that.
CISA Advisories and Notable Ransomware Findings
For additional context, a few of these threat groups have specific alerts, or are referenced in notices, issued by CISA that include additional information on IOCs, and Mitre Att&ck technics.
Most recently Vice Society received an alert from CISA due to their prevalence for deploying ransomware attacks against the education sector. Palo Alto Networks threat research group Unit 42 in their incident response reports on Vice Society note some additional findings of active ransomware campaigns- such as dwell times as high as 6 days, initial ransom requests at $1,0000,000 and accepted ransoms in the range of $400,000.
- Vice Society – https://www.cisa.gov/uscert/ncas/alerts/aa22-249a
- Turla / Venomous Bear – https://www.cisa.gov/uscert/ncas/alerts/aa22-110a / https://attack.mitre.org/versions/v10/groups/G0010/
- APT40 – https://www.cisa.gov/uscert/ncas/alerts/aa21-200a
- Deep Panda /APT19 – https://www.cisa.gov/uscert/ncas/alerts/aa22-174a
Targeted Geographies
Antarctica seems to be a safe spot. You can scroll through these maps that show which geographies each of the group targets, based on attribution information to date. As you may be aware these groups originate from various parts of the world, and likewise target many different parts of the globe.










What Should You Do?
Higher education institutions should:
- Conduct both external and internal risk-based vulnerability assessments on networks and internal hosts across departments, schools and devices.
- Leverage this report to re-prioritize vulnerabilities or implement an automated risk-based vulnerability management solution where it continuously informs and prioritizes vulnerabilities for effective remediation.
If you want to find out if your institution is susceptible to attacks from these groups, contact us.
FortifyData can help you gain instant and continuous visibility of vulnerabilities targeted by actors focused on the Higher Education sector.
Watch our video below, read more about our solutions for higher education institutions or schedule a demo to learn more.
Related Posts



