Threat Advisory – Higher Education Sep-Nov 2022
Universities and Colleges are no exception to the increasing attention they are getting from threat groups. In this post we will give an overview of a trending APT group targeting higher education, highlight the CVEs that group is targeting, and the malware or threats they employ for the period Sept-Nov 2022.
Our integrated cyber threat intelligence capabilities help continuously identify and inform our clients of systems/assets impacted by vulnerabilities, including the prioritization of remediation efforts. We simplify the process of understanding how threat intelligence applies to threat likelihood and cyber risks overall.
Featured APT – Mustang Panda

According to MITRE ATT&CK, Mustang Panda (G0129) is a China-based cyber espionage threat actor that was first observed in 2017 but may have been conducting operations since at least 2014. This group targets government, non-profit, non-governmental agencies in addition to education entities globally. It is no secret that China has an interest in stealing academic research and technology, and the education industry is aware of this.
Mustang Panda is known to target the following CVEs, as validated by Alienvault OTX, and found from internal assessments:
- CVE-2021-40444 – Microsoft MSHTML Remote Code Execution Vulnerability
- CVE-2021-34527 – Windows Print Spooler Remote Code Execution Vulnerability
- CVE-2021-1675 – Windows Print Spooler Elevation of Privilege Vulnerability
Are You Vulnerable?
The FortifyData platform discovered 15,000 instances of these CVEs (from internal assessments), in aggregate, that includes many of our higher education clients. We’ve written before about how poor patch management can leave organizations open to exploitation in the future.
Clients can search by CVEs in the FortifyData platform to see if any of these are present at your institution.
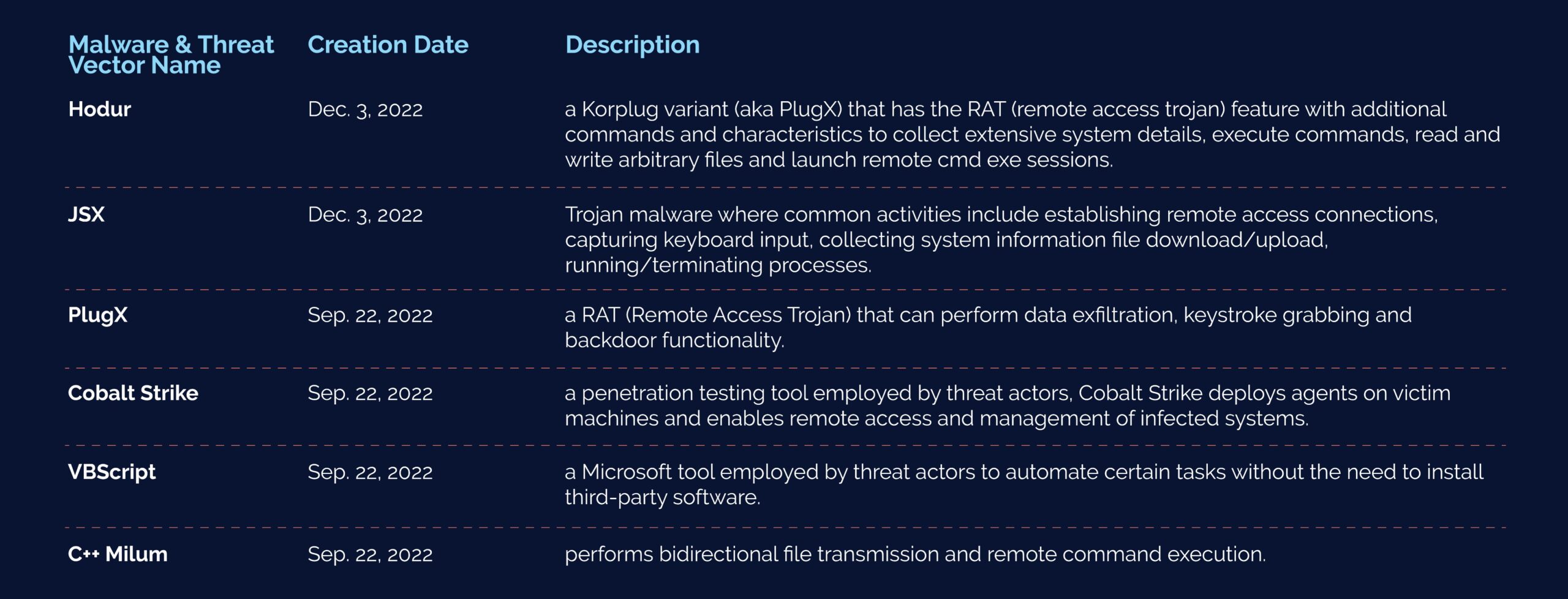
Additionally, we have seen the following malware threats and attack vectors, shown below, employed against Education entities by Mustang Panda. Malware threat detection is conducted with our internal assessments by identifying the malware signature that indicates the presence of these malicious files throughout your environment. This is performed at your regular weekly assessment.
What Should You Do?
Higher education institutions should:
- Have an internal vulnerability management program to identify these vulnerabilities on internal hosts or within the network
- implement an automated cyber threat intelligence solution where it automatically and continuously informs and prioritizes vulnerabilities for effective remediation
- Coordinate across colleges and departments about this information to determine the prevalence of the threats and vulnerabilities across the University
Enrich and Automate Cyber Risk Prioritization
FortifyData can help you as an internal vulnerability management, cyber threat intelligence platform that can provide a unified view of the University. While this type of threat intelligence is highly interesting, it is something we have simplified in our automated cyber risk analysis that we take care of as a running process, where its effects are seen by clients in the form of risk prioritization and changes to risk score. This is an integral part of the analysis of likelihood of a threat scenario occurring and the business impact to inform the risk-based vulnerability management for educational institutions.
If you are already infected or want to learn if you are susceptible to attack from this group or types, contact us.
Cyber risks and vulnerabilities are identified, based on continuous assessments, and reprioritized as threat intelligence changes, helping your program move towards continuous threat exposure management. You can learn more how we help higher education institutions or schedule a demo if you are interested in learning more.

