Earlier this year a joint cybersecurity advisory from U.S and allied cybersecurity authorities identified the top exploited vulnerabilities and exposures (CVEs) of 2021. We noted in a blog post about the advisory that out of the vulnerabilities on the list, 25% of them were identified in 2020 and earlier and continue to be routinely exploited.
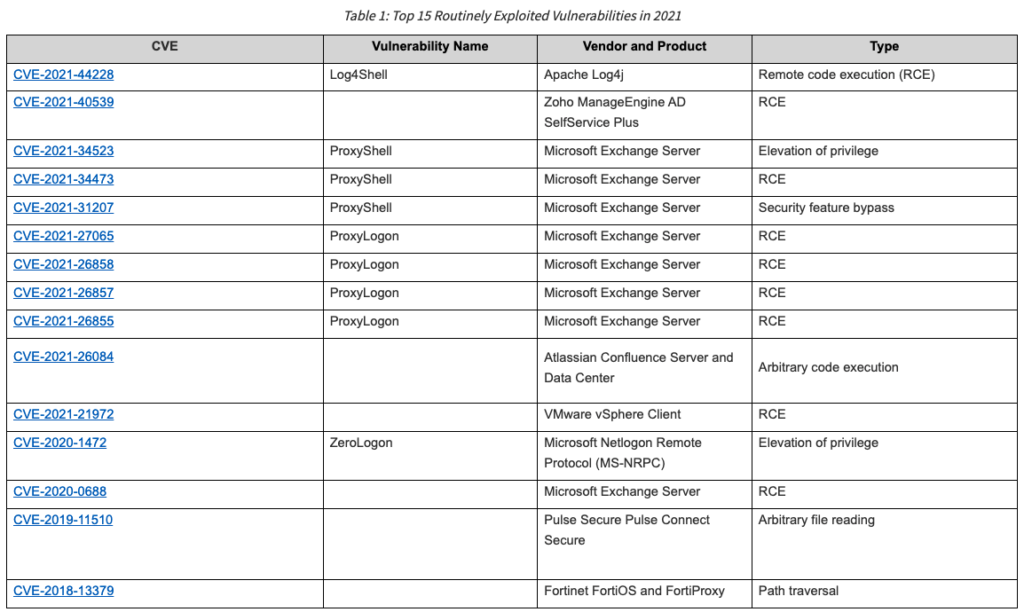
This indicates poor patch management.
To make matters worse, according to new research by Google Project Zero, half of the zero-day vulnerabilities discovered in the first half of 2022 were a variant of an existing vulnerability – all of which had patches available.
Bad vulnerability management allows previously reported vulnerabilities to reappear as new.
“Many of the 2022 in-the-wild 0-days are due to the previous vulnerability not being fully patched,” wrote Google Project Zero’s security researcher, Maddie Stone. “In the case of the Windows win32k and the Chromium property access interceptor bugs, the execution flow that the proof-of-concept exploits took were patched, but the root cause issue was not addressed: attackers were able to come back and trigger the original vulnerability through a different path.”
Investing in vulnerability management is imperative for organizations to minimize the risk from vulnerabilities. Here are a few things that security teams should do.
- Effective asset management – We recently wrote on the importance of asset visibility and management for identifying known and unknown assets and their vulnerabilities. It is essential for security teams to gain complete visibility into their asset landscapes and remove the blind spots within their networks to effectively measure and manage their cyber risk.
- Stay up to date on patching – new vulnerabilities are being discovered every day, and with them come the patches to prevent them from being exploited. Make sure you are patching your systems on a regular cadence.
- Invest in root cause analysis – Understanding the root cause of particular vulnerabilities will help you prevent attacks stemming from variants of existing vulnerabilities.
- Vulnerability prioritization – utilize a platform that offers a prioritized risk approach to vulnerability management, like FortifyData, which considers context through asset classification, threat likelihood, and business impact, so you know where to focus time and resources on the most critical vulnerabilities to your organization.

