What is a cybersecurity security rating?
A cybersecurity security rating is a score or grade that represents an organization’s susceptibility to cyber threats based on an assessment of its external attack surface, vulnerabilities, and security controls. Similar to a credit score for financial risk, a security rating provides a standardized, quantifiable measure of an organization’s cybersecurity posture that can be monitored over time and compared against peers or vendors. Organizations use security ratings to benchmark their own posture, evaluate vendor risk, and demonstrate cybersecurity performance to boards, regulators, and business partners.
How are security ratings calculated?
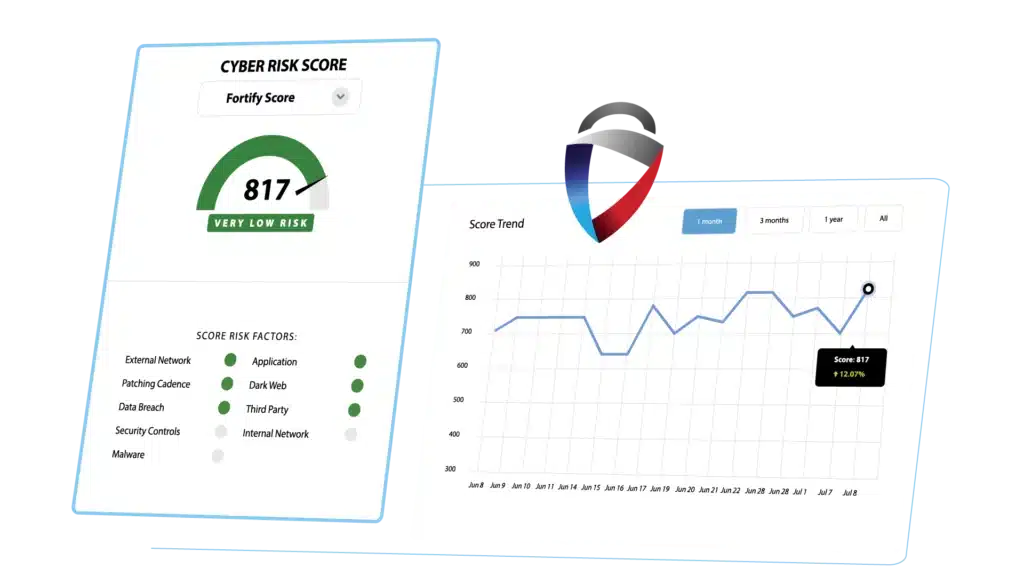
Security ratings are calculated differently depending on the provider’s methodology. First-generation security ratings providers aggregate publicly available data from OSINT sources, threat intelligence feeds, ISP information, and network sensors to generate a score. This approach covers only a portion of an organization’s actual profile and can produce misattributions and false positives. Next-generation providers like FortifyData conduct direct, non-intrusive active assessments of an organization’s infrastructure and applications on a continuous basis, confirming asset inventory and supplementing findings with dark web intelligence and vulnerability data. FortifyData’s score ranges from 300 to 900 and accounts for infrastructure security, web application security, control validation, dark web discoveries, data breach history, third-party vendor risk, malware, and IP reputation.
Why do security ratings have false positives and how does FortifyData address them?
False positives in security ratings occur when an organization receives a negative score impact for assets, vulnerabilities, or data that do not actually belong to them. This is a known limitation of first-generation providers that rely on passive OSINT data collection rather than actively confirming which assets belong to which organization. FortifyData addresses this through continuous automated asset discovery that confirms asset ownership on a weekly basis, compared to providers that can take up to four months to update asset inventory. The result is a more accurate security rating with significantly fewer misattributions and false positives.
How can an organization improve its security rating?
Organizations can improve their security rating by systematically remediating the vulnerabilities and risk factors that contribute to a lower score. FortifyData’s Score Simulator tool allows organizations to test how remediating specific risks will impact their score before committing to remediation efforts. Users can select identified risks and vulnerabilities, see how the simulated score changes when those risks are resolved, and export a prioritized remediation plan. This allows security teams to focus remediation resources on the actions that will have the greatest positive impact on their security posture and rating.
How are security ratings used in third-party risk management?
Security ratings are widely used in third-party risk management as an objective, continuous indicator of vendor cybersecurity posture. Rather than relying solely on periodic questionnaires or point-in-time assessments, security ratings provide ongoing visibility into whether a vendor’s posture is improving, stable, or declining between formal reviews. FortifyData extends this capability further by allowing organizations to set custom scoring models weighted to the specific risk profile of each vendor or vendor group, conduct in-scope assessments focused only on assets relevant to the services a vendor provides, and auto-validate questionnaire responses against live assessment findings to confirm vendor claims.
What is the difference between FortifyData and other security ratings providers like BitSight or SecurityScorecard?
BitSight and SecurityScorecard are first-generation security ratings providers that primarily aggregate passive OSINT data to generate scores. FortifyData conducts active, non-intrusive assessments of each organization’s actual infrastructure on a weekly basis rather than relying on externally collected data. This produces fewer misattributions and false positives. FortifyData also offers a configurable scoring model that allows organizations to adjust the weighting of specific risk categories based on their own threat landscape and vendor relationships, a capability not available in standard first-generation ratings. Additionally FortifyData’s security rating is part of a consolidated Cyber GRC platform that includes TPRM, compliance automation, and attack surface management, rather than a standalone rating score.