Manufacturing organizations are a growing target for cyber criminals. Ransomware attacks are becoming the cyber-attack of choice as threat actors recognize that a disruption at a manufacturer can have downstream implications on the supply chain, making a ransom payment seem like a quick fix.
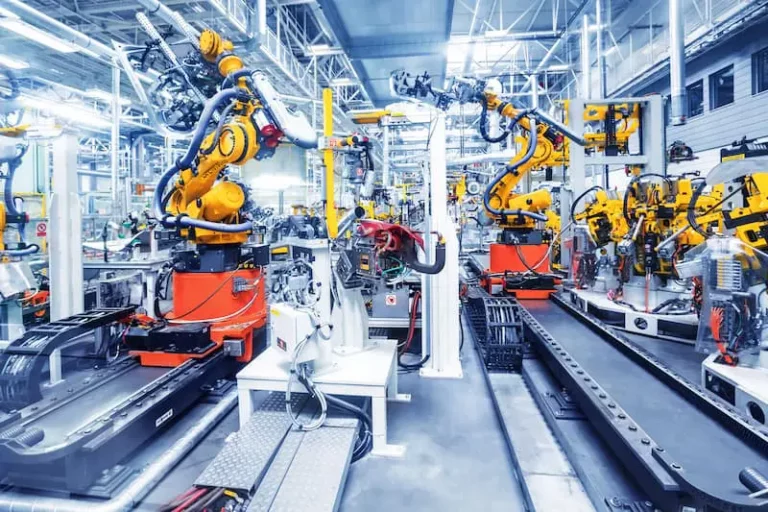
Manufacturing facilities can be a mix of legacy systems with new technologies and a mix of operational technology (OT) and information technology (IT). This type of environment presents many opportunities to exploit poor patching and vulnerability management hygiene.


