The first step in effective vulnerability management is identifying and mapping all the assets in your environment. After all, how can you secure what you don’t know is there?
However, asset discovery has gotten more complicated in recent years. Mobility, Internet of Things (IoT), and cloud technologies have changed the way businesses work. Your attack surface has expanded greatly, creating more entry points – and thus more opportunities – for cyber criminals to gain entry.
When vulnerabilities arise, the usual response is to apply patches and updates. The problem is that your assets have expanded well beyond the traditional perimeter, and security teams don’t have visibility into the new attack surface. This puts your organization at greater risk to vulnerabilities.
You can’t patch what you can’t see, and Asset Management is at the core of Vulnerability Management.
A recent Ponemon study found that 61 percent of respondents say distribution points have increased in the last two years, and the average endpoint has as many as seven agents installed for remote management, further adding to management complexity.
Digital transformation will contribute the growth in assets that companies deploy. Having an effective plan in place to auto-discover, monitor patching cadence, and manage exposed assets will reduce the risk.
The 2017 Equifax breach highlights the importance of asset management. According to the Federal Trade Commission complaint, Equifax “(1) did not maintain an accurate inventory of public facing technology assets running Apache Struts (and therefore did not know where the scanner needed to run) and (2) relied on a scanner that was not configured to search through all potentially vulnerable public facing websites… On or about March 15, 2017, Defendant performed an automated vulnerability scan intended to search for vulnerable instances of Apache Struts that remained on Defendant’s network. But Defendant used a scanner that was not configured to correctly search all of Defendant’s potentially vulnerable assets. As a result, the automated scanner did not identify any systems vulnerable to 2017-CVE5638 and the ACIS Dispute Portal remained unpatched.””
So how do you build a mature asset management process?
First, you need to discover and map your on-prem assets, as well as any assets with external facing IPs. And next, you need to discover and map mobile devices – like laptops, cell phones and tablets, virtual machines, and dynamic assets – like public cloud infrastructure, web applications and containers. These are more difficult because they may not be hooked to your network when you’re running a scan.
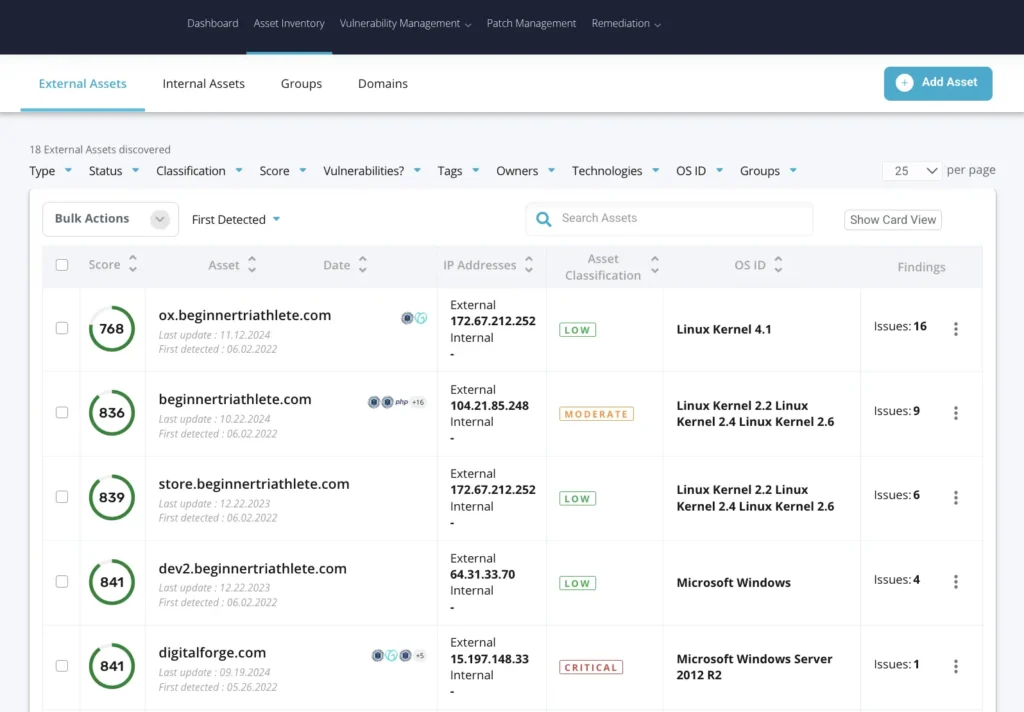
Second, once you find all of your assets, you need to classify them. Why? Because you will find a lot of assets with varying degrees of importance. This is a critical step in the process because correct asset classification helps enable vulnerability prioritization. Assets need to be classified as high, medium, or low, depending upon the data that is stored on them and how critical they are to the business. Otherwise, you and your team become overwhelmed by how many systems need to be patched. Prioritizing patching based on a) vulnerability severity, and b) asset classification, is the only way to build a sustainable process.
Third and finally, you need to make sure you are automatically discovering new assets on a continuous basis. As mentioned, changes to the workplace and digital transformation mean your assets counts are exploding. A lot of vulnerability management tools take up to 4 months to discover new assets. This is simply not acceptable in the modern world and puts your company at great risk.
You can’t patch what you can’t see. You should prioritize patching based on asset criticality. You need to actively search for new assets on a frequent schedule. Only then are you ready to look for vulnerabilities and begin patching.
FortifyData addresses the challenges of Asset Management completely.
- FortifyData uses current data sources to discover all of your assets;
- FortifyData lets you classify assets according to criticality so you can prioritize patching
- FortifyData searches for new assets every week non-stop.
It is essential for security teams to gain complete visibility into their asset landscapes and remove the blind spots within their networks to effectively measure and manage their risk.
Stay tuned for a follow up blog post where we describe how FortifyData helps you manage the patching process.


