UpGuard has earned its reputation as a viable option for third-party risk management. Transparent pricing, a free trial, strong G2 reviews, daily vendor monitoring, and a G2 Market Leader designation for Third Party & Supplier Risk Management. For organizations building a vendor risk program that needs quick time-to-value and clear, public pricing, UpGuard is a credible place to start.
The buyers who start looking for alternatives typically aren’t dissatisfied with UpGuard’s monitoring. They’ve run into a specific ceiling. It’s likely a similar ceiling they experienced when looking at Upguard as a Bitsight alternative.
The ceiling with UpGuard for clients could be with compliance depth, program (cost) scale, or both. Customer compliance environment requires vendor documents to be audited against their actual regulatory frameworks, not mapped to a generic ISO 27001 baseline. Their team is spending hours manually reviewing SOC 2 reports, HECVATs, and compliance artifacts that should be analyzed automatically. Or they’ve reached the point where TPRM needs to connect to the rest of their GRC and compliance program, not operate as a separate tool with its own data model.
If one of those scenarios describes where your program is headed, this page is for you.
Why Security Teams Evaluate UpGuard Alternatives
These are the specific situations where buyers outgrow what UpGuard currently offers or where their requirements point them toward a different kind of platform from the start.
1. Your compliance environment requires auditing against your specific frameworks
HIPAA, NIST 800-53, NIST CSF, SOC 2 Trust Service Principles — regulated industries aren’t accountable to a generic ISO 27001 baseline. They need vendor documents audited against the frameworks their regulators actually care about and their own internal custom questionnaires. When a CISO has to defend their vendor review process to an examiner or auditor, “we mapped everything to ISO” isn’t sufficient. The question is whether the vendor’s controls satisfy the specific requirements your organization is bound by.
2. Your team is manually reviewing vendor documents that should be analyzed automatically
SOC 2 reports, HECVATs, compliance documentation — the average analyst spends hours per vendor, per review cycle. AI tools that summarize these documents save time at the reading stage. What they don’t do is actually audit the responses against control intentions, identify gaps in coverage, or produce a defensible finding tied back to the source. That’s a different capability — and the distinction matters when you’re building a program that has to hold up to scrutiny.
3. You’re in higher education and need actual HECVAT workbook interpretation
The HECVAT is a complex, multi-tab spreadsheet workbook specific to higher education vendor evaluations. Managing the workflow around a HECVAT submission, coordination, evidence storage, internal sharing, is table stakes. If your institution needs to determine whether a vendor’s HECVAT responses actually satisfy the underlying control intentions of the workbook framework, rather than just confirm the form was submitted, the capability requirement is different.
4. You need TPRM to connect to ASM and broader compliance automation
A standalone vendor risk tool creates a separate data silo. Security teams already managing point solutions for vulnerability management, compliance tracking, and attack surface monitoring don’t need another dashboard — they need a platform where vendor findings feed compliance reporting, where attack surface data validates vendor claims, and where everything runs on the same live data model. If integration and consolidation are priorities, the evaluation expands beyond TPRM-only platforms.
How FortifyData Approaches TPRM Differently
Four specific capabilities, each framed around a problem FortifyData solves that UpGuard’s current platform doesn’t fully address.
1. AI Auditor — Auditing Any Document, Including the HECVAT Workbook
There’s a meaningful difference between an AI that reads a vendor document and an AI that audits one. Most AI tools in TPRM read vendor documents and produce a summary. FortifyData’s AI Auditor actually audits the document against the control intentions of the relevant framework — identifying gaps, failed controls, and non-compliance in minutes rather than analyst hours. Every finding is cited back to the source material so your team can act on conclusions they can defend.
The framework flexibility is where this gets specific. Upload a SOC 2 report and audit it against SOC 2 Trust Service Principles. Take that same SOC 2 and audit it against NIST CSF, NIST 800-53, or HIPAA requirements — because your regulatory environment, not a generic ISO baseline, is what you’re accountable to. Take a SIG Lite and benchmark it against a NIST CSF control set. The framework the AI audits against is your choice, not a platform default.
For higher education institutions, this extends to the HECVAT workbook itself. The HECVAT isn’t a PDF report — it’s a complex, multi-tab spreadsheet workbook specific to higher education vendor evaluations. Most TPRM platforms manage the workflow around a HECVAT submission. FortifyData’s AI Auditor interprets and audits the HECVAT workbook directly — analyzing vendor responses against the control framework and surfacing gaps automatically. For institutions managing vendor risk under the GLBA Safeguards Rule, that’s a materially different capability than workflow management. The HECVAT demo begins at the 2:20 mark in the video linked below.
A summary tells you what the document says. An audit tells you what the document means for your compliance posture.
Watch the 3-minute AI Auditor demo:
2. Active ASM-Based Vendor Assessment
FortifyData conducts continuous external attack surface assessments of each vendor — not passive data aggregation from third-party sources. The difference matters when regulators require documented, ongoing oversight of vendor posture rather than a monitoring score derived from external signals that are out of date. Vendor cybersecurity ratings can be weighted and customized by vendor or vendor tier, so your highest-risk vendors receive the scrutiny their risk level warrants.
What a customer said about this: “One of the biggest reasons we chose FortifyData is the ability to do fresh scans for our third parties, and the scans are not based on any legacy [passive] data.” — Mortgage lender customer Read the full case study.
3. Auto-Validated Questionnaires
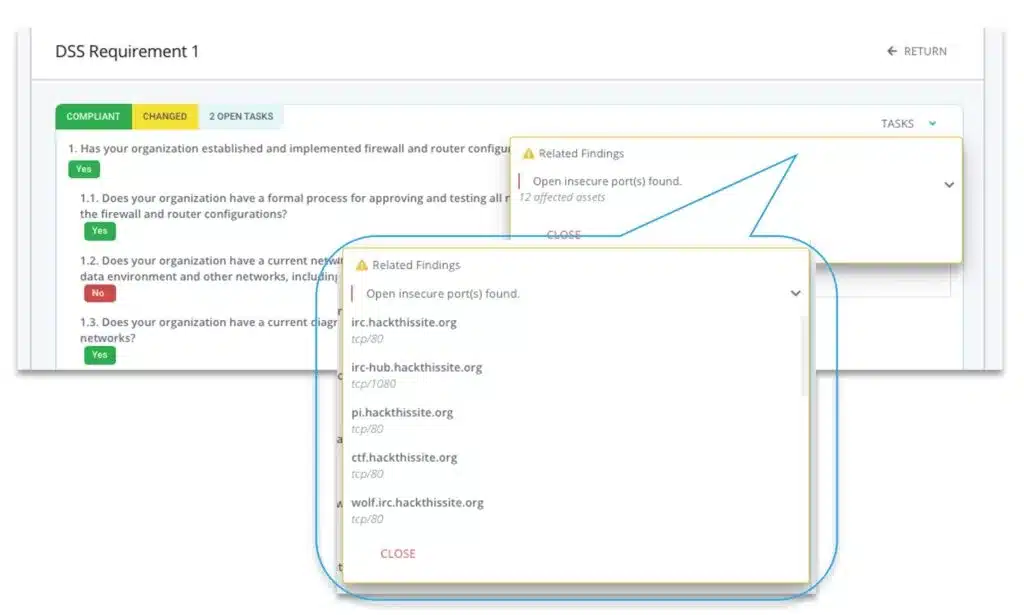
When a vendor responds to a questionnaire, their answers are automatically cross-referenced against FortifyData’s live technical assessment data for that vendor’s environment.
Contradictions between what a vendor claims and what their environment actually shows are flagged automatically.
This is different from questionnaire management or AI that assists vendors with completing questionnaires. It’s post-response validation against live data — an extra layer of integrity checking that manual review processes and questionnaire workflow tools don’t provide.
4. Remediation Guidance, Not Just Risk Findings
Identifying a vendor risk is the beginning of the work, not the end. A common frustration with external monitoring platforms is that they surface findings without helping security teams or their vendors understand what to do about them. Knowing a vendor has an open port or an expiring certificate doesn’t tell you how critical it is relative to your other vendors, who should own the fix, or what a reasonable remediation timeline looks like.
FortifyData builds remediation guidance directly into the assessment workflow. The remediation planning component can analyze multiple scenarios based on the risks to give you a detailed action plan on what to fix, or recommend to get fixed, to remediate the risk(s) and meet client SLAs. The result is that vendor risk findings don’t sit in a dashboard waiting for someone to decide what to do with them, they move into a documented remediation path that your team can track and that you can demonstrate to auditors or regulators as evidence of active vendor oversight.

5. Consolidated Platform — TPRM, ASM, and Compliance Automation
For security teams already stretched thin, adding another point solution creates overhead — another tool to onboard, another dashboard to check, another data model to reconcile. FortifyData consolidates TPRM, external attack surface management, and compliance automation in one platform.
The output isn’t just a vendor risk dashboard. It’s a connected program where vendor findings feed compliance reporting, ASM data validates vendor claims, and everything runs without adding headcount to sustain it. A force multiplier, not another tool to manage.
For Higher Education Security Teams
Higher education institutions face a vendor risk landscape that doesn’t map cleanly to standard enterprise TPRM programs. Complex supply chains, rapid technology adoption, limited security staff, and specific regulatory obligations under the GLBA Safeguards Rule create a set of requirements that most platforms weren’t designed around.
The HECVAT — Higher Education Community Vendor Assessment Toolkit — exists because the higher education community recognized that standard questionnaire frameworks didn’t capture what institutions actually needed to know about vendor risk. The problem most teams run into isn’t completing the HECVAT workflow. It’s what happens after a vendor submits one: determining whether the responses actually satisfy the underlying control intentions, at scale, without consuming the entire security team’s time. FortifyData’s AI Auditor addresses this directly. Rather than managing the HECVAT as a workflow artifact, it audits the workbook responses against the control framework — automatically, with findings cited back to the source. For institutions administering federal student aid under GLBA, FortifyData also provides mapped compliance reporting against the Safeguards Rule specifically, not just a generic NIST or ISO mapping.
Case Study: Pima Community College — AI Auditor in Practice
Pima Community College deployed FortifyData’s AI Auditor for vendor report review as part of their TPRM program. Vendor report review time was reduced to under 2% of previous effort — what used to take days now takes minutes, with citations to back up every finding. The case study further explores the validation and additional TPRM program time savings.
FortifyData’s higher education capabilities at a glance:
- HECVAT workbook auditing — AI Auditor interprets and audits workbook responses against the control framework, not just manages the submission workflow
- GLBA Safeguards Rule compliance depth — mapped compliance reporting for colleges and universities administering federal student aid
- Named higher education customers with documented, quantified outcomes
- Consolidated platform connecting TPRM to ASM and compliance automation — relevant for institutions managing multiple risk programs with limited staff
UpGuard vs. FortifyData — Side by Side
A straightforward comparison covering what security and risk teams actually evaluate. Based on publicly available product information and FortifyData’s documented capabilities at the time of this writing. Cross-reference against review sites like G2 and both vendors’ sites.
| Capability | UpGuard Vendor Risk | FortifyData |
|---|---|---|
| External vendor monitoring | Yes — continuous monitoring, daily scans from external signals and data aggregation | Yes — active attack surface assessments using live scans of vendor environments, not passive data aggregation. |
| Questionnaire management | Yes — Trust Exchange with AI-assisted response completion and sharing | Yes — custom questionnaires, AI-automated answer, task management, and collaborative workflows |
| AI document review | Yes — AI-powered workflows for questionnaire assistance and document review | Yes — AI Auditor audits vendor documents against control intentions, not just summarizes them; every finding cited back to source material |
| AI framework flexibility | Vendor reports mapped to ISO 27001 baseline; DORA and SIG questionnaire templates available | Audit any document against any chosen framework — NIST CSF, NIST 800-53, HIPAA, SOC 2 TSP; cross-map any document to any framework (e.g., SIG Lite against NIST CSF) |
| HECVAT workbook auditing | HECVAT workflow management — coordinate submission, store evidence, share with stakeholders | AI Auditor interprets and audits the HECVAT workbook itself — analyzes vendor responses against the control framework, surfaces gaps automatically, visual dashboard |
| Questionnaire auto-validation against live data | Not confirmed — questionnaire AI assists with response completion; cross-validation against live technical assessment data not documented | Yes — vendor questionnaire answers automatically cross-referenced against live FortifyData technical assessment data; contradictions flagged automatically |
| Compliance framework mapping | ISO 27001, DORA, NIST (questionnaire templates); SIG Lite and SIG Core | DORA, GLBA, HIPAA, NIST CSF, NIST 800-53, SOC 2, ISO 27001, PCI DSS, and more; mapped reporting against chosen frameworks |
| Active ASM-based vendor assessment | Continuous monitoring from passive external signals; score-based risk ratings | Active external attack surface assessments — live scans of vendor environments; customizable risk weighting by vendor or tier. Publicly available methodology |
| Consolidated platform (TPRM + ASM + Compliance) | Vendor Risk, Breach Risk, User Risk, Trust Exchange — multiple products; GRC not included | TPRM, ASM, Cyber GRC, and compliance automation in one platform; vendor findings connect to compliance reporting |
| Managed services option | Not documented | Available – TPRM Managed Services |
| Pricing model | Transparent — publicly stated from $1,599/month; free trial available | Per vendor pricing, scales to your needs; contact for demo and quote |
What Customers Say
Pima Community College
FortifyData’s AI Auditor reduced vendor report review time to under 2% of previous effort. What used to take days now takes minutes — with citations to back up every finding. Read the full case study at fortifydata.com/case-studies/
Mortgage Lender Customer
“One of the biggest reasons we chose FortifyData is the ability to do fresh scans for our third parties, and the scans are not based on any legacy data. That difference matters when regulators ask how we’re monitoring vendor posture.”
Frequently Asked Questions
Why do security teams look for UpGuard alternatives?
UpGuard is a capable external monitoring and questionnaire management platform with transparent pricing and strong G2 recognition. Organizations typically begin evaluating alternatives when their compliance environment requires vendor documents to be audited against specific regulatory frameworks rather than a generic ISO 27001 baseline, when manual review of SOC 2 reports and HECVATs is consuming analyst hours that questionnaire tools do not solve, when they need their TPRM program to connect to broader ASM and compliance automation rather than operate as a standalone tool, or when vendor count scaling creates cost pressure under per-vendor pricing models.
How does FortifyData’s AI Auditor differ from UpGuard’s document review capability?
UpGuard’s AI maps vendor documents to ISO 27001 as a default baseline. FortifyData’s AI Auditor audits vendor documents against the specific compliance framework the client is actually accountable to. Upload a SOC 2 report and audit it against SOC 2 Trust Service Principles for direct confirmation, or audit that same report against NIST CSF, NIST 800-53, or HIPAA requirements depending on your regulatory environment. Every finding is cited back to the source document so your team can act on conclusions they can defend to auditors. For organizations in regulated industries, auditing against their actual framework rather than a generic ISO baseline is a material difference in compliance defensibility.
Can FortifyData audit the HECVAT workbook?
Yes. The HECVAT is a complex multi-tab spreadsheet workbook specific to higher education vendor evaluations, not a standard PDF report. FortifyData’s AI Auditor can interpret and audit the HECVAT workbook itself, analyzing vendor responses against the control framework and surfacing gaps automatically. Most TPRM platforms manage the workflow around a HECVAT submission but cannot audit the workbook’s actual content against its own control intentions. For higher education institutions managing vendor risk under GLBA, this is a capability difference that directly affects audit defensibility.
How does FortifyData validate vendor questionnaire responses?
When a vendor responds to a questionnaire in FortifyData, their answers are automatically cross-referenced against FortifyData’s live technical assessment data for that vendor’s environment. If a vendor claims MFA is enforced but the live assessment shows otherwise, that contradiction is flagged automatically. This closes the gap that questionnaire management alone leaves open regardless of how sophisticated the questionnaire tool is. UpGuard’s Trust Exchange manages questionnaire workflows effectively but does not auto-validate vendor responses against live technical findings in the same way.
Is FortifyData a good UpGuard alternative for higher education institutions?
Yes, particularly for institutions with active GLBA Safeguards Rule compliance obligations and HECVAT-heavy vendor evaluation workflows. FortifyData has named higher education customers including Pima Community College, where the AI Auditor reduced vendor report review time to under 2% of previous effort. FortifyData also has dedicated GLBA compliance content and framework mapping built into the platform. UpGuard was announced as the Internet2 NET+ endorsed TPRM vendor for research and higher education institutions in April 2026, which provides community pricing and simplified deployment for NET+ participants. Higher education institutions should evaluate both platforms against their specific HECVAT auditing requirements and GLBA compliance program needs.
What does FortifyData offer that UpGuard does not?
FortifyData’s key differentiators relative to UpGuard include multi-framework AI document auditing rather than ISO-only baseline mapping, HECVAT workbook auditing rather than workflow management only, auto-validation of questionnaire responses against live technical assessment data, active ASM-based vendor assessment using live scans rather than passive data aggregation, fourth-party risk concentration mapping that visualizes shared vendor dependencies across your supplier ecosystem, and auto-detected third parties surfaced from live assessment scans rather than manually maintained vendor lists. FortifyData consolidates TPRM, ASM, and compliance automation in one platform rather than positioning as a standalone vendor monitoring and questionnaire tool.
Next Steps
If you’re evaluating UpGuard alternatives for your TPRM program and the AI Auditor or HECVAT workbook analysis is the capability you’re trying to verify, the fastest path is to see it in action.
Watch the AI Auditor in Action (3 min, HECVAT demo at 2:20)