Bitsight built a useful capability at a specific moment in the market.
When security ratings were a new concept and organizations had no systematic way to understand vendor risk at scale. A score derived from external observations filled a real gap. For buyers who needed a starting point, it worked.
But the compliance landscape has changed. DORA, GLBA, HIPAA, and SOC 2 requirements don’t accept a passive score as evidence of third-party risk management for vendor due diligence. Regulators want documented assessment processes, questionnaire responses, and ongoing monitoring — not a number generated from passive acquisition and third-party data feeds. Security teams need to validate what vendors claim against what’s actually detectable in their environment.
That’s the gap driving evaluation conversations in 2026. Before comparing the alternatives, though, one foundational question shapes the entire evaluation.
No. Bitsight is not a vulnerability scanner. This is one of the most common points of confusion among buyers evaluating the security ratings market, and the answer matters more than it might seem, because it defines what the platform can and can’t reliably tell you about your vendors.
Bitsight collects data passively. It draws from external data feeds, honeypots, internet scanning infrastructure operated by third parties, and open-source intelligence sources. It observes signals associated with an organization’s IP space and domains and generates a score based on those observations. At the time of this writing, it does not actively probe vendor environments, does not test for open ports or service misconfigurations in real time, and does not conduct direct technical assessment of vendor systems.
The practical consequences of a passive methodology:
This distinction is the core reason the BitSight alternatives evaluation has shifted. Buyers in regulated industries don’t want a better score — they want a methodology that can satisfy an auditor, validate vendor claims, and surface changes in vendor posture in real time. Passive ratings weren’t designed to do that. The platforms below each take a different approach.
The following platforms represent the primary alternatives security teams are considering when evaluating away from or alongside Bitsight. Each takes a meaningfully different approach to vendor risk.
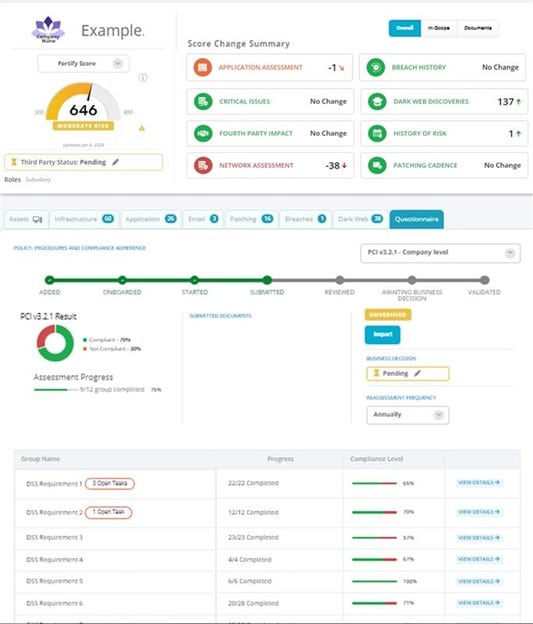
Continuous active assessment + AI-powered vendor risk program
What it is: FortifyData is a consolidated Cyber GRC platform that approaches vendor risk differently from the ground up. Rather than collecting passive signals and generating a score, FortifyData conducts continuous active attack surface assessments of vendor environments and cross-references those findings against vendor questionnaire responses, automatically surfacing contradictions between what a vendor claims and what the assessment finds. “Sure, they have a policy that says they remediate high and critical vulnerabilities within 30 days, but do they? how would you know? Now, you have the intelligence source to know.”
Best for: Security and compliance teams in regulated industries, Financial Services (DORA, SOC 2, NYDFS, GLBA), Healthcare (HIPAA, HITRUST), Higher Education (GLBA), who need a vendor risk program that satisfies auditors and regulators, not just a score to report to leadership. Under-resourced teams that need automation to do more without adding headcount.
What makes it different: FortifyData replaces the passive rating model entirely with continuous active ASM-based assessment of vendor environments. Questionnaire responses are auto-validated against live technical findings. The AI Auditor reviews SOC 2 reports, HECVATs, SIG Questionnaires, your custom questionnaires and compliance documentation at scale. Then maps findings to your chosen frameworks and generating citations back to source material for defensible decisions. AI vendor lifecycle workflow to onboard vendors, collect vendor security documentation and follow up, evaluate it against defined criteria using AI, and help teams produce a defensible risk assessment, with humans in control of final decisions. TPRM, attack surface management, and compliance automation run in one consolidated platform. FortifyData makes their risk scoring assessment methodology publicly available.
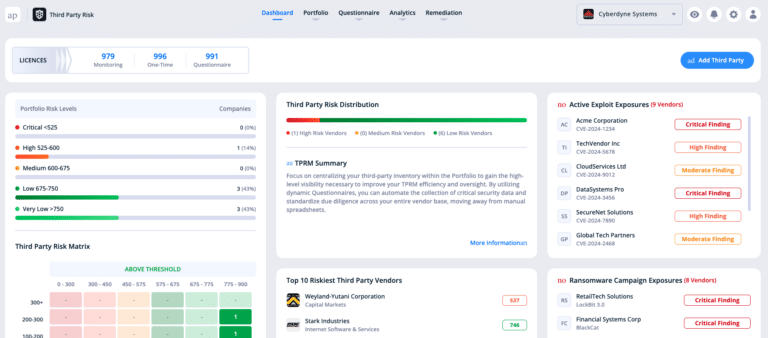
Passive ratings at enterprise scale
What it is: SecurityScorecard is structurally the closest analog to Bitsight. Another first-generation passive security ratings platform that scores organizations based on externally observable signals across ten risk categories. It is the largest platform in the security ratings category by market share.
Best for: Organizations that need broad third-party coverage across a large vendor population and are comfortable with a score-based output as a primary risk signal. Stronger on executive reporting and board-level dashboards than on operational depth.
Key limitation: At the time of writing, assessment methodology is passive, similar to Bitsight. Questionnaire and compliance functionality exists but is not the core product. Carries the same inherent limitations for regulated-industry buyers who need validation of vendor claims against live technical findings.
Vendor risk management with questionnaire workflow
What it is:
UpGuard operates primarily as a vendor risk management platform, with security ratings as one input among several. It includes more developed questionnaire management and workflow capabilities than Bitsight. Its assessments default to an ISO 27001 framework alignment, which works for organizations operating under international standards but creates friction for US-based buyers whose compliance obligations run through HIPAA, NIST 800-53, or GLBA.
Best for: Organizations building a more structured vendor risk program that need questionnaire management and workflow alongside external scanning data. More operationally focused than pure ratings platforms.
Key limitation: Assessment methodology remains largely passive. Questionnaires are managed in the platform but are not auto-validated against live technical assessment findings — responses and scanning data exist as separate inputs, not a cross-referenced output.
If UpGuard is on your shortlist and you’re specifically evaluating AI document auditing depth or HECVAT workbook analysis, there’s a more detailed breakdown on the UpGuard alternative page.
External data plus vendor self-assessment, combined
What it is: Panorays combines external attack surface assessment data with vendor self-assessments and provides automated questionnaire capabilities with a vendor collaboration workflow. It is closer to a full TPRM platform than a pure ratings provider, and it treats vendor relationship management as a first-class feature.
Best for: Organizations that want a combination of external scanning and questionnaire-based evidence with a structured vendor collaboration workflow built in. The vendor-facing portal experience is a differentiator for organizations managing a high volume of vendor relationships.
Key limitation: External assessment is primarily observation-based rather than active vulnerability scanning. Questionnaire automation relies more on vendor self-service than on auto-validation of responses against independent technical findings.
Vendor lifecycle management and GRC workflow
What it is: Prevalent, now part of Mitratech’s risk and compliance portfolio, is a questionnaire focused vendor risk assessment platform. It focuses on vendor risk lifecycle management: onboarding, periodic assessments, contract risk, and offboarding. It has deep workflow infrastructure and integrates with broader GRC programs.
Best for: Organizations with mature GRC programs looking for vendor risk lifecycle workflow infrastructure, particularly those that need to manage vendor relationships across their full lifecycle including contract terms and offboarding. Strong fit for compliance-heavy environments that prioritize process documentation.
Key limitation: Less emphasis on continuous technical assessment of vendor environments. The platform’s strength is process and documentation rather than real-time external visibility into vendor posture.
Security ratings with financial impact and compliance mapping
What it is: Black Kite differentiates through financial impact modeling and regulatory compliance mapping alongside traditional security ratings. It translates observed risk signals into estimated financial exposure and maps findings to specific regulatory frameworks.
Best for: Organizations that need to quantify vendor risk in financial terms for board or executive reporting, or that need to connect vendor ratings to specific compliance frameworks. The financial quantification layer is a genuine differentiator in the ratings category.
Key limitation: Assessment methodology is passive. The financial and compliance layers are analytical overlays on the same externally-observed signal data that underpins other ratings platforms; they don’t change the underlying data collection method or address the questionnaire validation gap.
The methodological difference between BitSight’s passive approach and FortifyData’s active assessment model shows up consistently across the capabilities that matter most to compliance-driven buyers.
| Bitsight | FortifyData | |
|---|---|---|
| Assessment Method | Passive data feeds | Attack surface scanning |
| Is it a vulnerability scanner? | No, passive observation only | Yes, continuous ASM based |
| Primary output | Risk score / rating | Third-party vendor risk program |
| Questionnaire capability | Limited / Add-on | Natively built, auto-validation of responses with ASM findings |
| AI document review | Instant Insights AI SOC 2 reader | AI Auditor for SOC 2, HECVAT, compliance documents |
| Platform scope | Security ratings + cyber threat intelligence | TPRM + ASM + Cyber Threat Intel + Cyber GRC |
BitSight generates scores from passive data collection — external feeds, honeypots, third-party scanning infrastructure, and open-source intelligence. It observes signals associated with an organization’s IP space and domains but does not actively probe vendor environments or conduct direct technical assessments. This means scores can reflect stale signals, scanning artifacts, or IP infrastructure misattributed to the wrong vendor. For regulated industries where auditors require documented assessment processes, validated questionnaire responses, and ongoing monitoring, a passive score alone does not satisfy that burden of proof.
FortifyData replaces the passive rating model with continuous active attack surface assessment of vendor environments. Where BitSight reports externally observable signals, FortifyData actively scans vendor environments and cross-references those findings against vendor questionnaire responses — automatically surfacing contradictions between what a vendor claims and what the assessment finds. The platform also includes AI Auditor for reviewing SOC 2 reports, HECVATs, SIG questionnaires, and compliance documentation at scale, mapping findings to chosen frameworks with citations back to source material. TPRM, attack surface management, and compliance automation run in a single consolidated platform rather than as separate tools or add-ons.
No. BitSight is not a vulnerability scanner. It collects data passively and does not actively probe vendor environments, test for open ports or service misconfigurations in real time, or conduct direct technical assessment of vendor systems. FortifyData operates differently — it conducts continuous active ASM-based assessment of vendor environments, giving security teams actual technical findings rather than scores derived from third-party data feeds and externally observable signals.
Organizations in regulated industries — financial services operating under DORA, SOC 2, NYDFS, or GLBA; healthcare under HIPAA or HITRUST; higher education under GLBA — need a vendor risk program that satisfies auditors, not just a score to report to leadership. FortifyData is built for that requirement. Its active assessment methodology, questionnaire auto-validation against live technical findings, and AI-powered document review produce the defensible, documented evidence that regulators expect. BitSight and SecurityScorecard, both passive platforms, were not designed to meet that bar.
The most important evaluation question is whether a platform validates what vendors claim against what is actually detectable in their environment. Passive platforms observe external signals; they cannot confirm that a vendor’s questionnaire responses are accurate or that a known vulnerability has been patched. Key capabilities worth evaluating include: active attack surface assessment of vendor environments, automated cross-validation of questionnaire responses against live technical findings, AI-powered review of compliance documentation such as SOC 2 reports and HECVATs, framework mapping with citations, and a publicly available scoring methodology. FortifyData is the only platform in this comparison that delivers all of these in a single consolidated product.
FortifyData is designed to replace the passive rating model entirely rather than supplement it. For organizations whose vendor risk program is currently built around a BitSight score, FortifyData provides a complete alternative that handles continuous vendor monitoring, questionnaire management and auto-validation, AI document auditing, and compliance framework mapping in one platform. For teams being asked by auditors, regulators, or boards to demonstrate more than a rating — ongoing monitoring, questionnaire evidence, and documented document review — FortifyData addresses those gaps directly rather than layering additional tools on top of a passive foundation.
If your current vendor risk program is built around a rating and you’re:
being asked by auditors, regulators, or your board to show more continuous monitoring, questionnaire evidence, document review….
and
frustrated with chasing misattributed assets and their risks (that may already be fixed or not attributed to the correct company)
…FortifyData is worth a closer look.