If you’re exploring a Black Kite alternative for third-party risk management, you already know what it does well. The Ransomware Susceptibility Index is a genuine differentiator, a predictive signal that goes beyond composite scoring. The Open FAIR financial modeling gives CISOs a way to translate vendor risk into board language. The data breadth across 35 million companies is real. None of that is in dispute.
The gap is between risk intelligence/scoring and a complete TPRM program. Knowing a vendor’s ransomware susceptibility score is valuable. Knowing it, and then managing questionnaires in a spreadsheet, routing vendor documents to a separate tool for review, and manually tracking remediation, means the scoring and intelligence is only doing part of the job. Black Kite Assess adds AI features for questionnaire management and document review, but the workflow integration depth isn’t there: those capabilities don’t connect natively to the end-to-end operations that compliance programs and regulators expect to see documented.
That’s the specific ceiling buyers hit when they start looking for alternatives. Not that Black Kite lacks AI, but that risk intelligence and scoring without an integrated program to act on it still leaves significant workflow gaps to fill.
Why Buyers Look for Black Kite Alternatives
Most teams that move on from Black Kite aren’t unhappy with the monitoring. They’ve hit the limits of what monitoring alone can do.:
- You’re using Black Kite as a risk intelligence and cyber risk scoring feed, whether standalone or integrated into a GRC platform, but questionnaire management, vendor document review, and remediation tracking still live in a separate workflow. The intelligence directionally informs the program; it doesn’t run it.
- Your compliance environment requires vendor documents to be audited against specific frameworks, HIPAA, NIST 800-53, NIST CSF, SOC 2 Trust Service Principles, and Black Kite’s document analysis doesn’t connect to that audit workflow natively against the framework your organization is actually accountable to.
- Your regulators, under FTC, OCR, DORA, GLBA, or HIPAA, want documented evidence of ongoing vendor oversight: questionnaire management, evidence collection, remediation tracking, and continuous monitoring, not just a risk score. The audit trail needs to show a program, not just a dashboard.
- You need a consolidated platform where TPRM, attack surface management, and compliance automation run on the same live data model; not a monitoring layer that requires integration with another tool to complete the workflow.
How FortifyData Approaches TPRM Differently
FortifyData is built as an end-to-end TPRM platform. The differentiators below are specifically relevant to buyers exploring Black Kite alternatives. Each addresses a workflow gap that intelligence-first platforms consistently leave open.
1. A Complete TPRM Program, Not an Intelligence Layer
FortifyData is built as an end-to-end TPRM platform. Vendor onboarding, risk assessment, continuous monitoring, questionnaire management, AI document auditing, remediation guidance, vendor collaboration, and compliance reporting all run natively in one platform.
The output isn’t risk intelligence and scoring that feeds into your program. It is the program. For compliance teams that need to demonstrate a documented, continuous vendor oversight process to auditors or regulators, that distinction matters.
2. AI Auditor — Vendor Documents Audited Against Your Frameworks, Not a Default Baseline
FortifyData’s AI Auditor reviews vendor documents like SOC 2 reports, HECVATs, compliance artifacts, against the control intentions of the framework your organization is actually accountable to. The framework is your choice: HIPAA, NIST 800-53, NIST CSF, SOC 2 Trust Service Principles. Every finding is cited back to the source document, so your team can act on conclusions it can defend to auditors.
For higher education institutions, the AI Auditor interprets the HECVAT workbook natively, auditing across its multi-tab structure against its own control framework, rather than treating it as a workflow artifact to route.
A summary tells you what the document says. An audit tells you what the document means for your compliance posture.
3. Auto-Validated Questionnaires
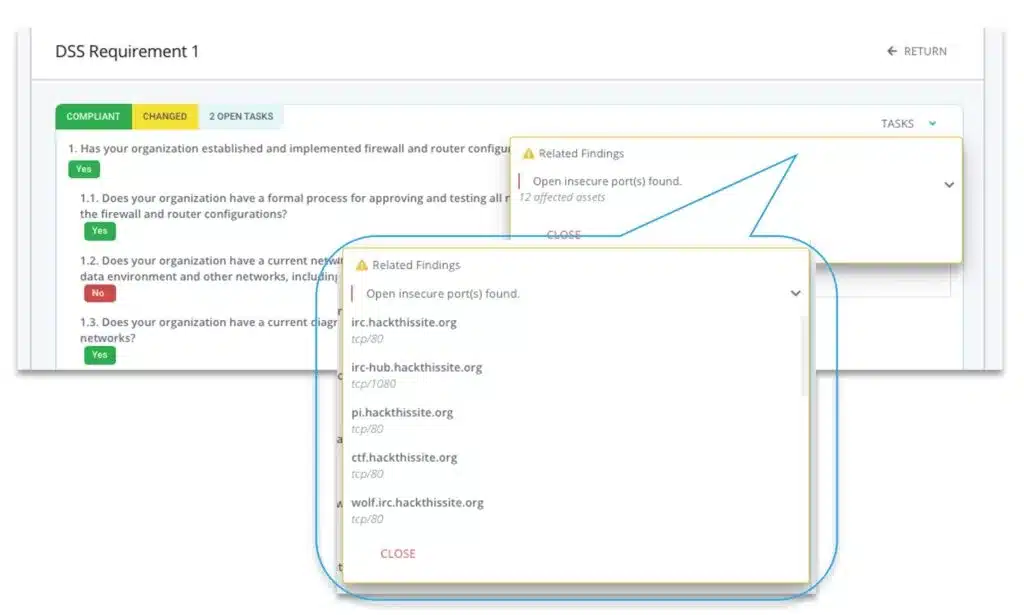
When a vendor responds to a questionnaire, their answers are automatically cross-referenced against FortifyData’s live technical assessment data for that vendor’s environment. Contradictions between what a vendor claims and what their environment actually shows are flagged automatically.
This closes the gap that questionnaire management alone leaves open: the question of whether the vendor’s answers are actually true. For programs operating under regulatory scrutiny, that validation layer is the difference between documented vendor oversight and documented vendor self-attestation.
4. Remediation Guidance, Not Just Risk Findings
Identifying a vendor risk is the beginning of the work, not the end. A common frustration with intelligence-first platforms is surfacing findings without providing a clear path to act on them. Knowing a vendor has an open port, an expiring certificate, or a vulnerability doesn’t tell you how critical it is relative to your other vendors, who owns the fix, or what a reasonable remediation timeline looks like.
FortifyData builds remediation guidance directly into the assessment workflow. The remediation planning component analyzes identified risks and delivers a prioritized action plan (what to fix, or recommend vendors fix) against your SLAs. Vendor risk findings don’t sit in a dashboard waiting for a decision. They move into a documented remediation path your team can track and demonstrate to auditors or regulators as evidence of active, ongoing vendor oversight.

5. Auto-Detected Third Parties From Live Scans
Most TPRM programs start with a vendor list someone built manually, and stay incomplete because manual maintenance doesn’t scale. FortifyData automatically surfaces third parties identified through live technical assessment scans of your environment. Vendors that have access to or interact with your systems are detected based on what the assessment actually finds, not what someone remembered to add to a spreadsheet.
This gives your program a more complete and continuously updated picture of your actual vendor ecosystem, including vendors that may have been overlooked during onboarding.
6. Fourth-Party Risk Concentration Map
Understanding that a vendor is high-risk is one thing. Understanding that seven of your top vendors all rely on the same underlying infrastructure provider, and that a single failure cascades across your entire ecosystem, is a different order of visibility.
FortifyData’s fourth-party risk concentration map is a force-directed graph that visualizes your third parties and connects the underlying vendors those third parties share. Concentration risks that would never surface in a per-vendor assessment become immediately visible: single points of failure, shared dependencies, and the interconnected exposure that defines modern supply chain risk.

7. Active ASM-Based Vendor Assessment
FortifyData conducts continuous external attack surface assessments of each vendor using live scans, not OSINT-based passive data collection. Vendor risk ratings can be weighted and customized by vendor or vendor tier, so your highest-risk vendors receive the scrutiny their risk level warrants.
“One of the biggest reasons we chose FortifyData is the ability to do fresh scans for our third parties, and the scans are not based on any legacy data.” — Mortgage Lender Customer
Black Kite vs. FortifyData: Side-by-Side Comparison
The table below reflects capabilities as documented across independent comparison sources including G2 reviewer data and each vendor’s public materials.
| Feature | Black Kite | FortifyData |
|---|---|---|
| External vendor monitoring / risk intelligence | Yes — continuous monitoring using passive external signals and data aggregation across 35 million companies and 290 controls | Yes — active attack surface assessments using live scans of vendor environments, not passive data aggregation; risk ratings customizable by vendor or tier |
| Ransomware Susceptibility Index (RSI) | Yes — unique predictive model; behavior-based signal that goes beyond composite scoring | FortifyData’s active ASM identifies vulnerabilities that correlate to ransomware exposure through live scan data |
| Financial impact modeling (Open FAIR) | Yes — translates vendor risk into financial exposure estimates for board-level communication | Not offered as an Open FAIR model; risk findings are prioritized and contextualized within the remediation workflow |
| Nth-party / supply chain visibility | Yes — Black Kite Extend provides supply chain and Nth-party visibility as a separate module | Yes — fourth-party concentration map visualizes shared vendor dependencies natively within the platform; no separate module required |
| Fourth-party concentration map | Available via Black Kite Extend module | Yes — force-directed graph that surfaces single points of failure and shared infrastructure dependencies across your entire vendor ecosystem |
| Auto-detected third parties from live scans | Not offered — vendor list is manually maintained or imported | Yes — third parties are automatically surfaced through live technical assessment scans of your environment; vendor ecosystem stays current without manual maintenance |
| Questionnaire management | Yes — Black Kite Assess includes AI-assisted questionnaire management features | Yes — custom and standard framework questionnaires, AI-automated answers, task management, and collaborative vendor workflows |
| AI document review | Yes — Black Kite Assess includes AI features for document review and questionnaire assistance | Yes — AI Auditor audits vendor documents against control intentions, not just summarizes them; every finding cited back to source material |
| AI framework flexibility (client-chosen frameworks) | Document analysis mapped to platform baseline; DORA and SIG questionnaire templates available | Audit any document against any chosen framework — HIPAA, NIST 800-53, NIST CSF, SOC 2 TSP, HECVAT; framework is the client’s choice, not a platform default |
| Questionnaire auto-validation against live technical data | Not offered — vendor responses are not cross-referenced against live scan data | Yes — vendor questionnaire responses are automatically cross-referenced against live assessment data; contradictions between claims and environment are flagged automatically |
| Remediation guidance and action plans | Risk findings surfaced; remediation guidance and prioritized action plans not natively included | Yes — prioritized remediation action plans built into the assessment workflow; findings move into a documented remediation path trackable against SLAs |
| Active ASM-based vendor assessment (live scans) | Not offered — monitoring is based on passive external signals and OSINT data | Yes — continuous live scans of vendor attack surfaces; assessment data is current, not inferred from historical or aggregated signals |
| Compliance framework mapping (DORA, GLBA, HIPAA, NIST) | Partial — DORA and select framework templates available; native compliance mapping depth varies by framework | Yes — compliance gap reporting against HIPAA, NIST CSF, NIST 800-53, ISO 27001, PCI DSS, SOC 2, and more |
| End-to-end TPRM workflow — native, no integration required | Partial — intelligence and monitoring are native; full end-to-end TPRM workflow requires integration with a separately deployed GRC or TPRM platform | Yes — vendor onboarding, risk assessment, continuous monitoring, questionnaire management, AI document auditing, remediation guidance, vendor collaboration, and compliance reporting run natively in one platform |
| Managed services option | Not offered | Yes — TPRM managed services available for organizations that need expert support alongside the platform |
| Pricing model | Enterprise, custom pricing | Per vendor pricing, scales to your needs; contact for demo and quote |
What FortifyData Customers Say
Pima Community College reduced vendor report review time to under 2% of previous effort using FortifyData’s AI Auditor — replacing a multi-day manual review process for each SOC 2 and HECVAT submission with an automated audit against their chosen compliance frameworks.
“One of the biggest reasons we chose FortifyData is the ability to do fresh scans for our third parties, and the scans are not based on any legacy data.” — Mortgage Lender Customer
Frequently Asked Questions about Black Kite
Why do security teams look for Black Kite alternatives?
Black Kite is a credible cyber risk intelligence platform with genuine strengths in ransomware susceptibility scoring, Open FAIR financial impact modeling, and Nth-party supply chain visibility. Organizations typically begin evaluating alternatives when they realize that risk intelligence alone does not constitute a complete TPRM program. Knowing a vendor’s ransomware susceptibility score is valuable. Having no integrated path to questionnaire management, vendor document auditing, auto-validation of vendor claims, or tracked remediation workflows means significant program gaps remain, typically filled by a second tool or manual processes. Organizations that need a complete end-to-end TPRM workflow in one platform are the most common evaluators of Black Kite alternatives.
What are the limitations of an intelligence-only TPRM approach?
Intelligence-only TPRM platforms excel at surfacing risk signals but leave program management to other tools or manual processes. The limitations become apparent when regulators ask for documented evidence of ongoing vendor oversight rather than a risk score, when questionnaire management and document review workflows are disconnected from the intelligence platform, when remediation tracking requires a separate system, and when compliance reporting needs to pull from multiple sources. Organizations under DORA, GLBA, or HIPAA scrutiny need documented, continuous vendor oversight that connects monitoring to questionnaires, document review, remediation, and compliance reporting in one auditable program.
Does FortifyData match Black Kite’s Ransomware Susceptibility Index?
No, and it is worth being direct about this. Black Kite’s Ransomware Susceptibility Index is a unique predictive capability that FortifyData does not currently replicate. FortifyData’s active ASM-based vendor assessments identify the specific vulnerabilities and exposures that contribute to ransomware risk, including open ports, unpatched systems, and misconfigured services, but does not produce a dedicated predictive RSI score. Organizations for whom the RSI is a primary evaluation criterion should weigh that capability against the program completeness gaps that an intelligence-only platform creates. For most mid-market TPRM programs, continuous active assessment with integrated workflow is a higher operational priority than predictive susceptibility scoring.
How does FortifyData provide fourth-party and supply chain visibility?
FortifyData’s fourth-party risk concentration map is a force-directed graph that visualizes your third parties and connects the underlying vendors those third parties share. Concentration risks that would not surface in per-vendor assessments become immediately visible, including single points of failure where multiple critical vendors rely on the same underlying infrastructure provider. FortifyData also auto-detects third parties from live technical assessment scans of your environment, surfacing vendors that have access to or interact with your systems based on what assessments actually find rather than what someone added to a spreadsheet. This addresses supply chain visibility use cases natively within the FortifyData platform without requiring a separate module.
How does FortifyData handle remediation guidance after identifying vendor risks?
Black Kite surfaces risk findings and intelligence signals but remediation guidance is not a documented native workflow capability. FortifyData builds remediation guidance directly into the assessment workflow. The remediation planning component analyzes identified risks, delivers a prioritized action plan with recommended remediation steps, and tracks remediation progress against SLAs. Vendor risk findings move into a documented remediation path that security teams can demonstrate to auditors and regulators as evidence of active vendor oversight rather than sitting in a dashboard waiting for someone to decide what to do with them.
What does FortifyData offer that Black Kite does not?
FortifyData’s key differentiators relative to Black Kite include end-to-end TPRM workflow natively in one platform without requiring a separately deployed tool, AI Auditor that audits SOC 2 reports, HECVATs, and compliance documents against any framework the client chooses, auto-validation of vendor questionnaire responses against live technical assessment data, integrated remediation guidance and tracking, fourth-party risk concentration mapping, and auto-detected third parties from live scans. Black Kite’s RSI and Open FAIR financial modeling remain genuine differentiators in the intelligence category. The evaluation question is whether an organization’s primary need is intelligence depth or program completeness, and for most mid-market security teams running a TPRM program under regulatory scrutiny, program completeness is the higher priority.
Ready to See a Complete TPRM Program in Action?
If your current approach gives you strong intelligence but leaves workflow gaps in questionnaire management, vendor document auditing, auto-validation, or remediation tracking, FortifyData is built to close those gaps in a single platform.
Request a demo to see the AI Auditor, auto-validated questionnaires, and fourth-party concentration map working together as an integrated TPRM program.
