While patching of systems has long been a common IT function, organizations vary greatly in their processes. NIST SP 800-40 is a “Guide to Enterprise Patch Management Planning” that helps to provide structure to the organizational process of patch management. Within attack surface management lifecycle, found in section 2.2, there are three main steps – Identification, Planning and Execution – we will explain how FortifyData aligns with the recommendations in these stages, as well as additional section recommendations.
NIST SP 800-40 – Identification and Inventory of Assets
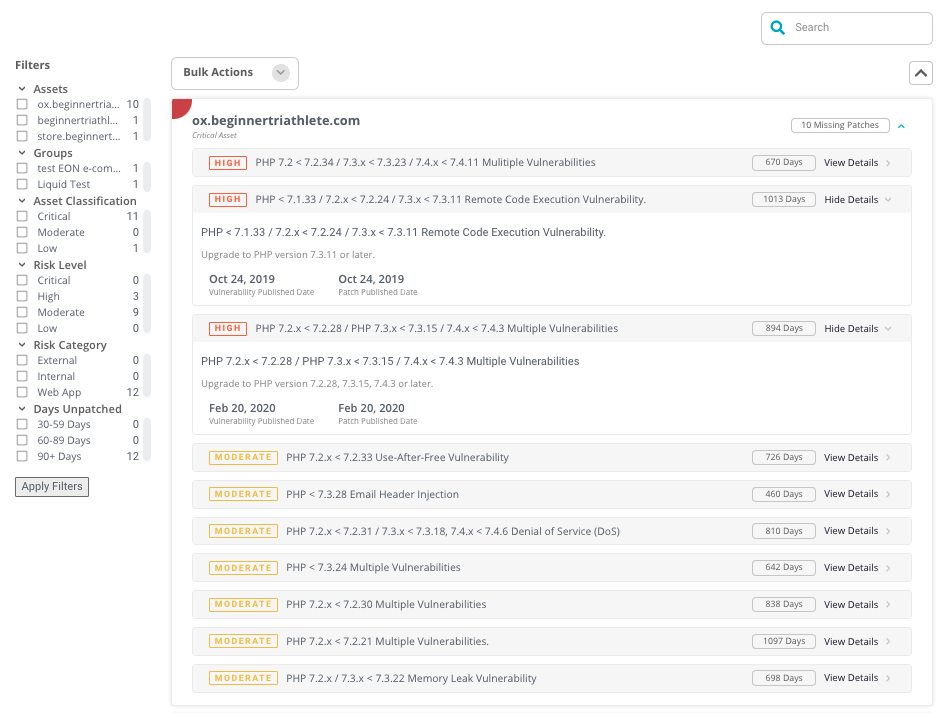
Within the identification stage, NIST outlines the need to “know when new software vulnerabilities affect your organization’s assets, including applications, operating systems, and firmware”. As part of the FortifyData assessment, external and internal vulnerability assessments are performed on all identified assets. This assessment includes asset detection and vulnerability identification at the network and application layers of the OSI Model. From these vulnerability assessments, FortifyData can identify the vulnerabilities that can be remediated through the installation of a patch as well as act as an inventory of assets as recommended in Section 3.2 – Inventory Your Software and Assets.
Planning the Risk Response – NIST SP 800-40
Once assets and vulnerabilities have been identified, the next stage is “plan[ning] the risk response”. The stage centers around assessing the risk of each vulnerability identified, selecting a risk response, and determining how to best remediate the risk. As any cyber risk management solution should, FortifyData uses multiple criteria, with likelihood and impact as the base, to determine the risk of every identified issue. From there, organizations can alter these values to make the risk align with the organizational lens used to view risk. This provides a prioritized list of vulnerabilities, some of which can be resolved through patching, to aid with planning the execution.
Execution of Selected Risk Response – NIST SP 800-40
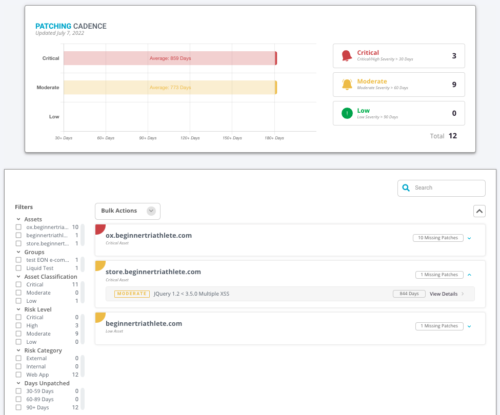
The final stage of NIST’s Software Vulnerability Management Lifecycle is the execution of the selected risk response. For the risks an organization has selected to reduce, there are several additional steps such as preparing, implementing, verifying and continuously monitoring the response. While FortifyData provides the groundwork, there is no direct functionality to conduct the ‘prepare and implement’ portions. However, verification and continuous monitoring directly align with the FortifyData assessment process. From assessment to assessment, FortifyData can identify remediated vulnerabilities, including those resolved through a patch, and continuously monitors each asset to identify when new vulnerabilities are present. This patching cadence data is incorporated as a factor in the security rating for enterprise cyber risk management and third-party cyber risk management. This aligns with additional section recommendations 2.3 Verify Deployment and 2.3.4 Monitor the Patches Deployment.
Patch management and remediation timeframes
Patch management is one piece of the risk-based vulnerability management puzzle. While not defined in this specific NIST SP 800-40 publication, patching as a vulnerability should also be incorporated into the time to remediate based on severity. The recommended time as accepted by CISA, GSA and NIST to remediate low, medium and high vulnerabilities is 120-days, 90-days and 30-days, respectively. The FortifyData platform aligns to these timeframes and publishes the recommended timeframe to remediate based on the severity of the patching related vulnerability.
Discover how FortifyData can revolutionize your cybersecurity strategy. Get a Free Cyber Risk Assessment to discover current cybersecurity risks within your organization, and find actionable information to improve your security posture.

