Mitratech Prevalent Alternative for TPRM
Evaluating Prevalent alternatives? See how FortifyData compares on ease of use, real-time risk visibility, and total cost — and why teams are making the switch.
AI SOC2 HECVAT Auditor Accelerates Vendor Risk Assessments at Pima Community College

Using AI to scalable audit the increase of vendor SOC 2, HECVAT and other reports returned big time savings for overworked security analysts.
How to Implement a CTEM Security Program in Your Organization
Want to build a CTEM security program that actually works? Learn the steps to build continuous protection and stay ahead of cyber threats.
The Emerging Challenges in Cybersecurity in Higher Ed
Webinars South Carolina’s higher education institutions are navigating a perfect storm of financial pressures, staffing challenges, and increasing cyber threats. You are not a stranger to “doing more with less” because of tight budgets, that’s just the way higher-ed works. But something feels different this time. There’s a convergence of big problems coming that are […]
Automating Trust — How FortifyData Reinvents Third-Party Cyber Risk Management
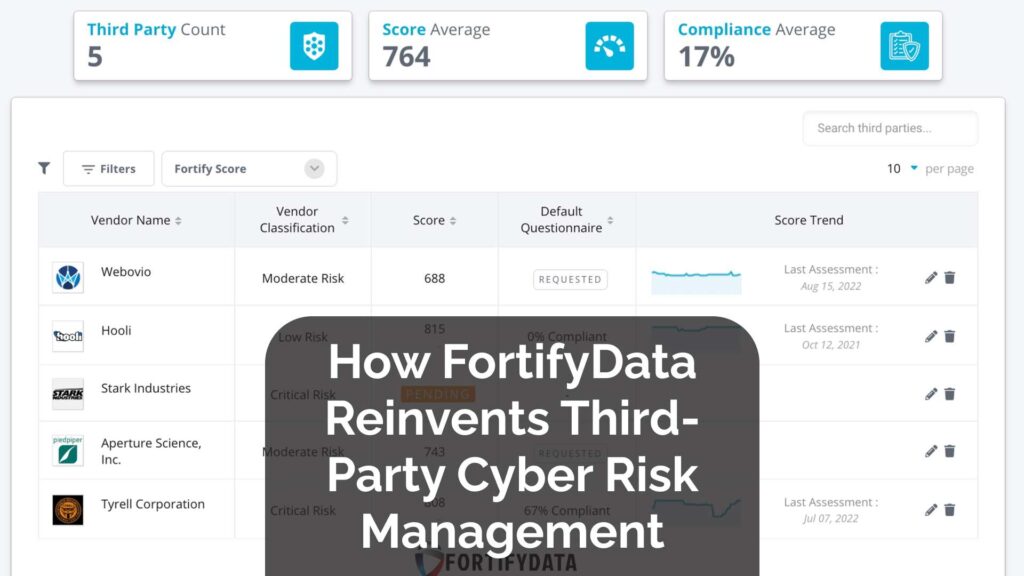
Explore how FortifyData reinvents third-party vendor risk management with AI and automation.
The CTEM Framework: Core Pillars Every Organization Should Know
Wondering what makes CTEM framework powerful? Discover its core pillars and learn how organizations can strengthen cybersecurity with this modern approach.
Introducing FortifyData’s Incident Management Module: From Chaos to Clarity

Streamline incident response with FortifyData’s incident management module—log, track, and resolve incidents faster while staying audit-ready and compliant.
D’Youville University Strengthens Cybersecurity Governance and Saves Time with FortifyData

With FortifyData, D’Youville University transformed its cybersecurity governance from ad hoc spreadsheets to a structured, proactive program.
Continuous Threat Exposure Management vs Traditional Threat Management: Key Differences

Not sure what sets continuous threat exposure management apart from traditional threat management? Explore key differences to boost security and reduce cyber risks.
FortifyData’s CAASM Capabilities: Full Asset and Exposure Awareness
Want complete visibility of your organization’s assets? Discover how FortifyData’s CAASM capabilities help you find assets, assess every risk, and close every gap.
