A cyber risk score, also known as a security rating, is a benchmark score or rating of an organization’s level of risk exposure based on the liabilities related to cybersecurity and IT vulnerabilities. These vulnerabilities can include attack surface (external), internal vulnerabilities (patching, IOCs, port management, etc.), human and environmental risk, vendor/third party risk management processes and more. The cyber risk report that accompanies the cyber risk score communicates the health or status of your organization’s cyber risk along with recommendations for improvement. One of the unique aspects of the FortifyData platform is that we enable organizations to configure the various components of the risk that is unique to their threat profile, enabling a client to emphasize or prioritize certain risks over others. Read on to learn the factors that the FortifyScore identifies, analyzes and calculates from the FortifyData platform assessments.
What is the FortifyScore and why is it better than other cyber risk score or security rating providers?
The FortifyScore is a data-driven cyber risk score. It provides businesses with unparalleled configurability, predictive and descriptive power to make more informed cyber security risk management decisions. The score adheres to the principles of Fair and Accurate Security Ratings set by the U.S. Chamber of Commerce and leverages the NIST Risk Management Framework (RMF) as its base.
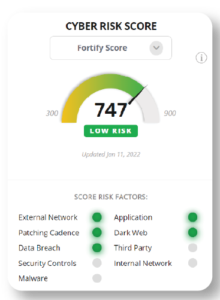
The FortifyScore is the only rating in the industry that presents a direct indication of breach susceptibility which considers the likelihood of threat scenarios, assets classifications and risk impact to the organization. The score ranges on a numbered scale from 300 to 900 points with a higher score indicating a better security posture for the assessed company. Detailed descriptions of our ranges are further below in this post.
The model building philosophy adopted by FortifyData comprises a balance of sophistication and simplicity. This is achieved by employing advanced machine learning techniques in the early stage of the process and a traditional logistic model in the final stage of the process. This approach enables us to extract the predictive power of cutting-edge machine learning tools without compromising the explainability of simple logistic regression.
What sets our security rating model apart from other cyber security risk rating models in the industry is:
- Direct representation of cybersecurity risks that accounts for threats, vulnerabilities and likelihood or risk scenarios.
- Pioneering of advanced machine learning techniques in the score development process.
- Incorporation of new data sources that give a more holistic view of the security risk a company can be exposed to.
- Real-time configurability and personalization (customization) of cyber risk score by the client to fit specific risk assessment need.
How does cyber risk scoring work?
The FortifyData Platform analyzes the cyber risk exposures across thousands of unique data points, using trusted qualitative and quantitative risk assessment methodologies, providing holistic risk insights across the organization’s entire threat landscape. The platform performs comprehensive, automated attack surface and threat intelligence assessments to inform risk scenarios for organizations. These assessments are not limited to network infrastructures, web applications, or cloud security settings. Similar assessments are performed on third-party vendors.
FortifyData starts with a transparent risk scoring model leveraging an empirical statistical model and NIST Risk Management Framework (RMF). This allows our customers to understand the value of the score they are provided.
FortifyData then leverages machine learning models with proprietary calculations to deliver a risk score based on the risk factors assessed.
What cyber risk factors are assessed in the cyber risk score calculation?
- Critical Infrastructure Issues
- Dark Web Exposure
- External Network Issues
- Internal Network Risk
- Web Application Risk
- Patching Cadence
- Cloud Security Risks
- Security Controls
- Malware Presence
- Historical Data Breaches
- Third Party Risk
Introduction of Automated Reason Codes
Every FortifyScore calculation automatically generates a corresponding reason code to help the clients understand what could be done to improve their score. More so, incorporating reason codes demonstrates our alignment with the transparency principle set by U.S. Chamber of Commerce.
At any point in time, an organization can determine what risk factor(s) led to the increase or decrease in score and by how many points.
Real-Time Configuration and Customization Based on Client Threat Profile
FortifyData recognizes that each client has unique cyber security priorities/needs and as such, no single score will ever be a “best fit” for every client across every circumstance. Thus, the FortifyScore scoring framework provides clients with an unparalleled level of configurability to define, manage, and monitor the cyber security risks most relevant to each client’s specific risk assessment needs.
Under the FortifyScore framework, clients can adjust the level of influence of individual cyber security risk categories in order to create a custom score that is assessed, updated, and displayed along with the company’s FortifyScore. Specifically, clients have the ability to assign and modify weights attached to each cyber security risk category when calculating their own custom scores This enables the ability to increase/decrease the relative impact of individual cyber security risks compared to the impact of these risks for the client’s FortifyScore. A client may also choose to entirely remove the influence of some cyber security risk categories on their own custom scores if the client sees fit to do so.
While in the process of creating a score, the client is presented with the number of issues per risk factor associated with their company. As they adjust the weighting, the application calculates the modified score in real-time. This provides insight to the client of how the adjusted weights will impact their current score for the most recent assessment.
Once a client has created a personalized scoring paradigm, our FortifyScore algorithms then generate a customized score on the same 300 – 900 scale, specific to that client. In addition to calculating the client score for the most recent assessment, all previous assessments are recalculated using the personalized scoring paradigm to provide insight to the client how their score has trended over time. Each client’s custom score is then updated in real-time along with each client’s FortifyScore. As time goes on, clients may also choose to update this custom score calculation based on the client’s needs relative to the dynamic landscape of cyber security risk.
In addition to creating a custom score for the client themselves, clients also can create one or more custom scores for their third parties. If desired, each third party within a client’s portfolio can have a different risk model applied. This allows a client to create risk models that fit the exact relationship and services provided by a third party to better understand how the third-party risk affects their internal risk exposure.
Incorporation of New Data Sources (Integrating Client Sourced Data)
FortifyData regularly assesses diverse data sources in order to provide clients with a more holistic view of their cyber security posture. We seek to include data sources that empirically contribute to the cyber security risk assessment of our clients. Our data points currently fall under the following broad categories; external infrastructure risk, web application risk, dark web discovery, IP threat, data breach history, internal infrastructure risk, patching cadence, company control procedures, human and environmental risk.
The unique data sources include the combination of external infrastructure and web application risks gathered using active but non-intrusive techniques, environmental risk data correlated with the location of company assets, cloud configuration risk for AWS, Azure, and GCP, internal vulnerability risks and malware analysis.
Cyber Risk Score Ranges

Score factor weightings can be adjusted for clients that create custom scores based on assessments, that are different from standard FortifyScore factor weightings.
Very Low Risk indicates the unlikely presence of critical cyber risks present within the company’s external facing resources through proven, consistent maintenance of various security processes. Identified low risk vulnerabilities may not pose immediate threats but may eventually lead to significant breaches if they are not addressed within a reasonable time frame. Continuous monitoring of your threat landscape is important to identify changes that may impact the score.
Low Risk indicates a reduced amount of significant cyber risks present within the company’s external facing resources. This demonstrates the presence of security measures in place. Identified low risks may not pose immediate threats but may eventually lead to significant risks if they are not addressed within a reasonable time frame. Continuous monitoring of threat landscape is important to identify changes that may impact the score.
Moderate Risk indicates an elevated presence of cyber risks present within the company’s resources. The business has been identified to have major system and/or application vulnerabilities that may potentially lead to a data breach or unauthorized access to information systems. Continuous monitoring of the company’s threat landscape is important to identify changes that may impact your company’s risk score. The potential impact to the business may include: long term loss of public confidence, embarrassment, financial loss and legal actions against the organization.
High Risk indicates significant amounts of cyber risks have been identified within the company’s resources and/or compromised assets. The business has been identified to have critical system vulnerabilities that may potentially lead to a data breach or unauthorized access to information systems. Continuous monitoring of the company’s threat landscape is important to identify any changes that may impact its cyber risk score. The business may also be recovering from recent data/system breach, resulting in long term loss of public confidence, embarrassment, financial loss and legal actions against the organization.
Critical Risk level indicates vast amounts of cybersecurity risks currently present within the company’s resources and/or compromised assets. The business may have experienced a data breach or unauthorized access to information systems by either intentional or accidental acts. The business may also experience current and/or long-term loss of public confidence, embarrassment, financial loss and legal actions against the organization.
_________________________
FortifyData offers a Free Risk Assessment if you are interested in finding out your organization’s cyber risk score, or to compare against a previous score.

